|
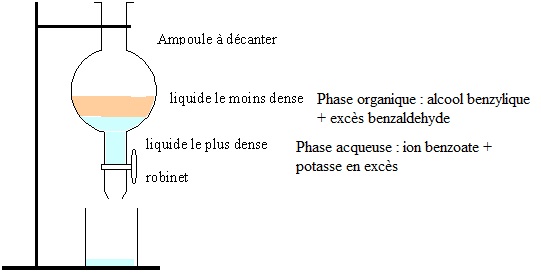
Synthèse de Cannizzaro, bac Métropole 2021. En poursuivant votre navigation sur ce site, vous acceptez l’utilisation de Cookies vous proposant des publicités adaptées à vos centres d’intérêts. ..
..
: Identify Alternate Data Streams within the RAR. Attackers often hide the real payload inside the ADS of a legitimate-looking file to evade standard antivirus scans. Based on available technical analyses and CTF (Capture The Flag) documentation, "Whitehat_Revenue.rar" is a malicious archive frequently used to demonstrate or exploit the vulnerability in WinRAR. Whitehat_Revenue.rar : Look for connections to Command & Control (C2) servers. Previous WinRAR exploits have been linked to exfiltrating browser logins to platforms like Webhook.site . Mitigation : Identify Alternate Data Streams within the RAR : The archive uses improper validation of file paths and Alternate Data Streams (ADS) to escape the user's selected extraction directory. : Look for connections to Command & Control (C2) servers : Check the system for new files in the Windows Startup directory or modified Registry keys (such as HKCU\Software\Microsoft\Windows\CurrentVersion\Run ). : While the user is distracted by the decoy, the exploit leverages the path traversal to drop a malicious payload (such as a .NET RAT or shell script) into a critical system directory like C:\Users\[Username]\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ .
|
||||||||
|
|
||||||||